Search News
Industry Portal
Popular Tags
How to Improve Cybersecurity for Industrial Control Systems
Author
Dr. Isaac Logic
Time
Apr 28, 2026
Pageviews
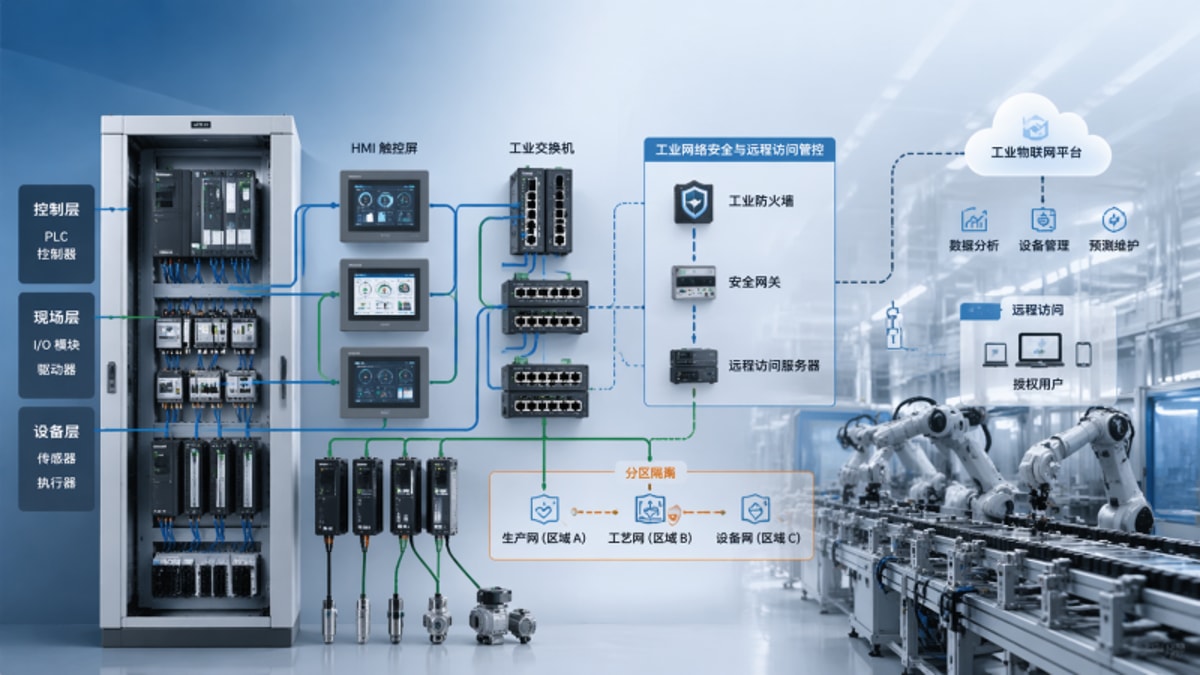
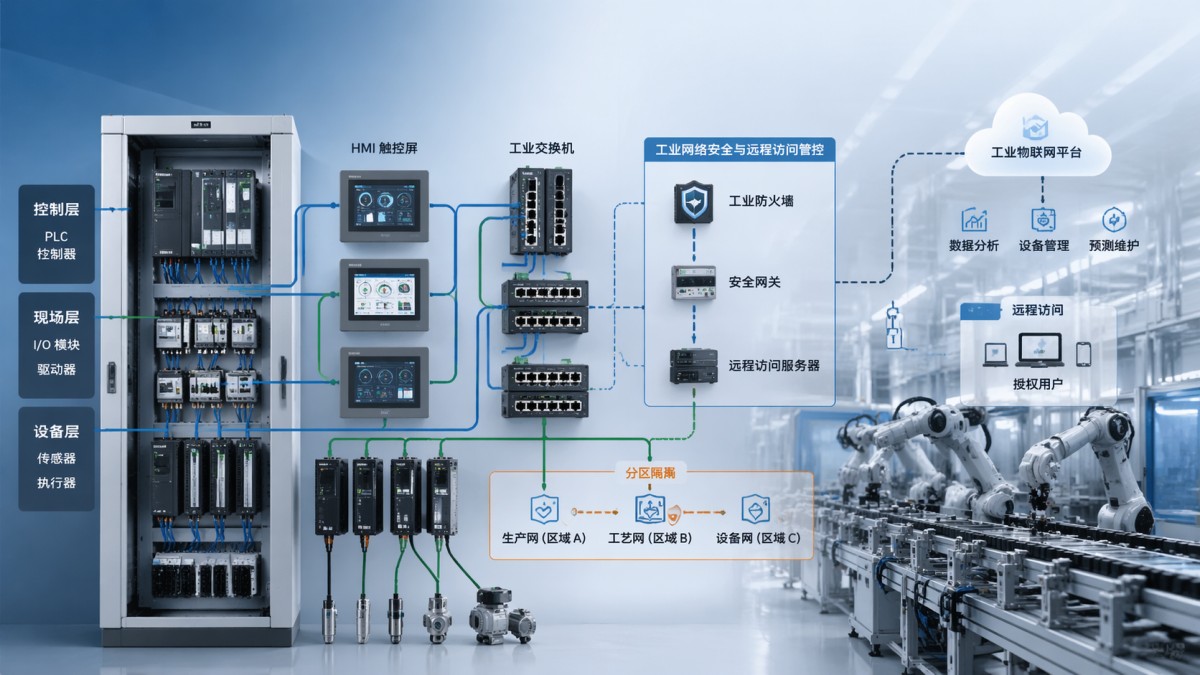
As smart factories become more connected, cybersecurity for industrial control can no longer be treated as a secondary concern. From PLC networks and HMI interfaces to remote monitoring and Industrial IoT platforms, every integration point introduces risk. This article explores practical ways to strengthen ICS security while helping engineers, buyers, and decision-makers balance resilience, compliance, and performance in modern automation environments.
Why industrial control system cybersecurity is now a plant-level business issue
Industrial control system cybersecurity is no longer only an IT concern. In modern manufacturing, a breach can interrupt batch production, disable motion control, corrupt process recipes, or force a controlled shutdown that takes 8–24 hours to recover from. For operators, the risk is unsafe process behavior. For procurement teams, the risk is buying incompatible security tools. For executives, the risk is downtime, compliance exposure, and delayed delivery commitments.
The challenge is structural. Industrial environments combine PLCs, SCADA, HMI panels, drives, robots, historians, MES, ERP connectors, and remote maintenance channels. Many assets were designed for reliability and long service life of 10–20 years, not for frequent patching. As a result, cybersecurity for industrial control systems must protect legacy equipment and new Industrial IoT endpoints at the same time, without disrupting deterministic control or real-time performance.
For cross-sector factories, the attack surface usually expands in 4 predictable ways: more networked machines, more vendor remote access, more software integrations, and more data exchange between OT and IT. A packaging line, a metalworking cell, and a process skid may use different protocols, but they often share the same weak points: flat networks, default credentials, unmanaged engineering laptops, and unclear ownership of updates.
This is where G-IFA adds value. By benchmarking automation hardware and industrial software across PLC & Control Systems, Industrial IoT & Software, Motion Control, Robotics, and fluid power systems, G-IFA helps technical teams evaluate cybersecurity readiness as part of engineering due diligence, not as an afterthought added after commissioning.
What makes ICS security different from office IT security?
In office networks, confidentiality often leads. In industrial networks, availability and process integrity usually come first. A delayed patch in an office PC may be acceptable; a delayed command to a safety-relevant controller may not be. That is why cybersecurity for industrial automation must respect scan cycles, deterministic communication, maintenance windows, and validated machine states.
- Production assets may run continuously for 16–24 hours per day, limiting patch windows.
- Legacy protocols may lack native authentication or encryption.
- Even a short interruption can affect quality, traceability, or operator safety.
- Multiple suppliers may share service responsibility, making governance harder.
Where are the biggest ICS cybersecurity risks in connected factories?
Most vulnerabilities are not hidden in exotic attack paths. They are found in common operational habits. Plants frequently connect engineering workstations to both enterprise and machine networks. Remote support tools may remain enabled after commissioning. Passwords may be shared across 3–5 HMI stations. Backup files may exist, but restoration may never have been tested on an actual spare controller.
The following matrix helps teams identify high-priority industrial control system cybersecurity gaps before they become production incidents. It is especially useful during plant expansion, line retrofits, supplier onboarding, and annual risk reviews.
A practical takeaway is that industrial cybersecurity maturity does not start with buying more software. It starts with segmentation, access control, backup integrity, and asset visibility. In many plants, solving these 4 areas reduces exposure faster than launching a broad, expensive security program with no OT prioritization.
The most overlooked exposure points during expansion and retrofit projects
During new line deployment or retrofit, security controls are often deprioritized to meet a commissioning window of 2–6 weeks. This creates blind spots that remain for years. Typical examples include unmanaged switch cascades, default service ports left enabled, engineering laptops without application control, and third-party gateways added without a formal risk review.
High-risk integration points to check first
- Remote maintenance appliances connecting machine builders to on-site PLC networks.
- MES, ERP, or cloud connectors pulling production data from SCADA or historian systems.
- USB-based firmware updates and recipe transfers between engineering stations and HMIs.
- Shared Windows hosts running visualization, logging, and administrative tools together.
For buyers and decision-makers, the lesson is simple: every new integration should be treated as a security design event. If the line adds one more data path, one more supplier, or one more remote support workflow, the cybersecurity review should be updated before start-up, not after the first production fault.
How to improve cybersecurity for industrial control systems without harming uptime
The most effective ICS security programs are phased. A realistic roadmap usually has 3 stages: visibility, control, and resilience. Stage one identifies assets, communication paths, and critical process dependencies. Stage two restricts access and segments traffic. Stage three hardens backup, recovery, monitoring, and incident response. This sequence helps plants improve security while maintaining production continuity.
For operators and maintenance teams, the goal is not abstract cyber maturity. The goal is to keep machines running in a known-good state. That means approved engineering changes, tested backups, role-based access, and maintenance procedures that do not bypass security controls under time pressure.
A practical 6-step implementation path
- Map all OT assets, including PLCs, HMIs, IPCs, switches, remote gateways, historians, and robot controllers.
- Classify assets by criticality: safety impact, production impact, and recovery difficulty.
- Segment networks into logical zones for cells, lines, and plant services.
- Control remote access with MFA, approval workflow, and session recording.
- Establish backup and restore validation on a scheduled cycle, such as every quarter.
- Run tabletop response drills so OT, IT, maintenance, and management know escalation steps.
This sequence is especially suitable for mixed-vendor environments because it does not assume one control brand, one software stack, or one site architecture. It focuses on governance and engineering controls that remain useful across robotics cells, PLC-based packaging lines, water treatment skids, and batch processing systems.
G-IFA supports this process by helping teams compare equipment and software from a systems perspective. That matters because cybersecurity for industrial control systems is often limited by integration behavior rather than by a single device specification. Knowing how a controller, gateway, drive, or software connector fits into a larger architecture reduces procurement mistakes.
Which controls should be prioritized first?
If budget or plant access is limited, prioritize the controls with the fastest risk reduction. In many facilities, that means 5 checks within the first 30–60 days: remove shared accounts, disable unused services, document all remote entry points, create offline backups, and isolate business systems from machine networks. These actions are modest in cost but significant in operational value.
What should buyers compare when selecting ICS cybersecurity solutions?
Procurement often fails when products are compared only by license price. In industrial environments, the more important criteria are protocol compatibility, deployment method, maintenance burden, vendor access control, logging depth, and recovery support. A lower-cost tool can become more expensive if it creates false alarms, requires frequent tuning, or cannot support legacy assets still needed on the line.
The table below is designed for B2B evaluation teams comparing industrial control system cybersecurity options. It can be used during RFQ preparation, site audits, or supplier review workshops involving operations, engineering, IT, and plant management.
A strong procurement decision aligns cybersecurity controls with production architecture. For example, a discrete manufacturing site with many robot cells may prioritize segmentation and remote access control, while a continuous process plant may focus first on availability, change management, and recovery validation. The same product shortlist rarely fits both equally well.
How decision-makers can avoid under-scoping the project
A common mistake is to budget only for software licenses and ignore 4 delivery layers: network redesign, policy development, user training, and recovery testing. In practice, implementation may involve 2–4 stakeholder groups and several maintenance windows. The better approach is to request scope clarity early: asset count, number of lines, remote access users, backup requirements, and validation milestones.
- Ask whether existing switches, firewalls, and engineering stations can support the design.
- Confirm whether the supplier has OT deployment experience, not just enterprise security experience.
- Request a phased rollout option for one line, one workshop, or one critical cell first.
Which standards and compliance frameworks matter for ICS cybersecurity?
No single standard solves every industrial cybersecurity requirement, but several frameworks are widely used to structure decisions. IEC 62443 is commonly referenced for industrial automation and control system security. ISO-based management practices may support governance, while CE, ISO, and other technical requirements may affect how equipment is integrated, documented, and validated in broader automation projects.
For buyers, compliance should not be treated as a checklist detached from real operations. The better question is: which controls are necessary for this plant, this architecture, and this supplier model? A machine builder with remote diagnostics, a multinational plant with centralized MES, and a brownfield site with aging PLCs will not have the same implementation path, even if they reference the same framework.
How to use standards without slowing the project
A practical method is to divide compliance into 3 layers. First, governance: roles, access approval, change control, and vendor accountability. Second, technical controls: segmentation, authentication, logging, hardening, and backup. Third, validation: documentation, testing, and periodic review every 6–12 months. This keeps the project actionable rather than theoretical.
G-IFA is particularly useful in this stage because it helps teams compare automation components and system architectures against international engineering expectations. When production directors or system integrators need to de-risk investments, they need more than generic cybersecurity advice. They need component-level transparency and a clear understanding of how digital and mechanical systems interact under real operating conditions.
Compliance questions to ask before approval
- What remote access control and audit trail are required by internal policy or customer contract?
- Which assets are safety-relevant or production-critical, and what recovery target is acceptable?
- What documentation must be handed over at FAT, SAT, and post-commissioning stages?
- How often will passwords, backups, and firewall rules be reviewed after go-live?
Common questions, mistakes, and next-step decisions
Many teams understand the need for cybersecurity for industrial control systems but hesitate on where to start. The answer depends on plant maturity. If there is no accurate asset inventory, start there. If remote access is uncontrolled, address that first. If backups exist but have not been restored in the last 12 months, recovery validation becomes urgent. Sequencing matters more than chasing every control at once.
How often should an ICS cybersecurity review be performed?
For most industrial sites, a formal review every 6–12 months is reasonable, with additional checks after major line upgrades, software integrations, or supplier access changes. High-change environments may need quarterly reviews of remote access logs, backup status, and network modifications. The right cadence depends on change frequency and operational criticality, not on a fixed calendar alone.
Can legacy PLC systems be protected without full replacement?
Usually yes. Full replacement is not always necessary. Many legacy assets can be better protected through segmentation, jump hosts, controlled remote access, application whitelisting on engineering stations, and stronger backup discipline. Replacement becomes more urgent when unsupported components create unacceptable recovery risk, incompatible integration risk, or repeated maintenance instability.
What are the most common buyer mistakes?
Three mistakes are especially common: treating OT security like office IT, buying tools before defining architecture, and assuming the machine builder owns long-term cybersecurity after handover. In reality, ownership often shifts across OEMs, integrators, plant engineering, IT, and operations. Clear governance prevents costly gaps during audits, incidents, and expansion projects.
Why choose a benchmark-driven partner before making a purchase decision?
Factories rarely struggle because there are no products available. They struggle because it is hard to compare equipment, software, standards alignment, and integration risk across multiple vendors. G-IFA helps technical and commercial teams evaluate industrial robotics, PLC & control systems, motion platforms, IIoT software, and fluid power infrastructure with a benchmark-driven approach tied to international engineering expectations.
If you are planning a line upgrade, selecting secure PLC and HMI architectures, reviewing remote maintenance risks, or preparing a plant-wide ICS cybersecurity roadmap, contact G-IFA for targeted support. You can consult on asset and protocol fit, product selection logic, delivery scope, compliance considerations, implementation phasing, recovery planning, and quotation alignment before committing budget or issuing a final RFQ.
Recommended News
- 2026/05/07Remote I O module wholesale: how much redundancy is enough?Remote I/O module wholesale: learn how much redundancy is enough to protect uptime, control costs, and improve reliability with practical procurement guidance.
- 2026/05/07Open source PLC trends are changing small-line automation choicesOpen source PLC trends are reshaping small-line automation with lower lock-in, faster integration, and scalable control choices. Discover what buyers should evaluate before upgrading.
- 2026/05/07What VFD suppliers rarely mention about motor heat and tuningvfd variable frequency drive supplier insights on hidden motor heat, poor tuning, and low-speed load risks—learn practical checks to prevent failures and extend motor life.
